Massive DoD DevSecOps standards push may aid enterprise IT
The Section of Defense has introduced a major new hard work to publish security benchmarks and best practices for governing administration DevSecOps and perhaps enterprise IT as effectively, SearchITOperations has discovered.
The hard work is led by Nicolas Chaillan, chief software program officer for the U.S. Air Drive, and co-lead for the Organization DevSecOps Initiative in the office environment of the Section of Defense (DoD) CIO. Chaillan explained he has invited much more than two dozen companies and open up source entities to participate in 7 subgroups inside the project, which include Microsoft, Purple Hat, VMware, StackRox, Pivotal, D2iQ, The Linux Basis, The Cloud Native Computing Basis, Sysdig, Rancher and Splunk.
“[The Section of Defense] generally has a different approach, wherever, for case in point, Purple Hat can create security steerage for RHEL or OpenShift — it can be generally just one firm, just one item,” Chaillan explained. “This will be the full Kubernetes ecosystem and community — all the Kubernetes distros, vendors and cloud suppliers we work with.”
The Cloud Native Computing Basis, StackRox, Sysdig and Rancher verified this 7 days that they are taking part in the project, which has not been publicly introduced prior to this report and as of however, has no official name. Other companies Chaillan cited could not right away be reached for remark.
Countrywide Institute of Requirements and Know-how (NIST) fellow Ronald S. Ross is also taking part as a co-lead with Chaillan, with strategies to increase DevSecOps steerage to present NIST SP 800-one hundred sixty systems security engineering benchmarks, and to publish new volumes that build a DevSecOps reference architecture.
NIST and the DoD doing work group will collaborate on best practices and security benchmarks paperwork, with the aim of manufacturing an early draft inside sixty to seventy five times, Chaillan explained. The group will use a Git repository to edit and keep the paperwork, which will be publicly accessible.
NIST has a lengthy history of doing work with community and private sector companies to build security benchmarks, but what helps make this hard work special is the focus on implementing security benchmarks to a particular use scenario in DevSecOps, NIST’s Ross explained.
“In the outdated times, the army and its contractors crafted systems that had been only utilised for army applications, which gave them a lead more than adversaries who didn’t have the identical technology,” Ross explained. “But there has been a technology explosion wherever most systems are dual-use, intended for the two governing administration and professional use — and adversaries have the identical technology.”
To secure the country, the DoD will have to build a lead in the use of cloud-indigenous systems and study how to stay ahead of adversaries with best practices, instead than an absolute specialized gain, Ross explained.
“This is the most important project I have been included with in much more than thirty a long time in the field of cybersecurity,” he included.
A opportunity DevSecOps template for enterprises
As governing administration businesses and private-sector enterprises increasingly use the identical open up source systems, several professional companies search to the governing administration, significantly the DoD, as the gold standard for cybersecurity, just one IT consultant explained.
“You can find a stating, ‘Nobody at any time obtained fired for using IBM,'” explained Jeremy Pullen, principal specialized consultant at Polodis, a electronic transformation consulting firm in Atlanta, who’s carefully following the DoD’s DevSecOps work, which include a not too long ago printed repository of hardened container images for typical use. “You can find a very similar self-confidence in using systems hardened to the benchmarks of the US governing administration.”
Pullen explained the breadth of the collaboration will also aid legitimize the DevSecOps principle as a established of practices, instead than tying it to any unique tool, seller or system utilised by particular household-name enterprise IT groups.
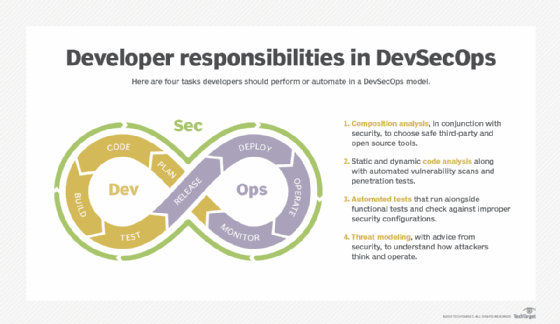
“The last two a long time, I have experienced to teach individuals about what DevSecOps is and isn’t — it can be not just using a tool from White Hat, Sonatype or Veracode,” he explained. “This paints a better photograph of DevSecOps as an space of follow instead than just utilizing somebody’s item.”
The hard work will also aid the governing administration much more effortlessly procure new systems, which could translate into enterprise procurement strategies, Pullen explained.
This project reflects a change in the federal government’s approach to tech, as effectively as a typical change toward open up source software program, and open up source awareness sharing, across the IT business, explained Shannon Williams, co-founder and president of Rancher, whose federal workforce will work on Kubernetes security benchmarks.
Other open up benchmarks, such as Middle for Net Security (CIS) benchmarks, already exist for this reason, but this project will enhance how they are connected to other DevSecOps applications and refine how protected software program is created, Williams explained.
“This isn’t just about hardening Kubernetes — it can be about how to establish a protected software program factory,” he explained. “It is really about how to function Kubernetes, in a established of living paperwork that can alter as new technology emerges.”
In addition to container and Kubernetes hardening for DevSecOps use, just one of the sub-groups in the DoD project will standardize a approach that generates ongoing authority to function for each and every software program alter developed by a governing administration company.
It is really a follow the Air Drive has already carried out below Chaillan, which suggests software program variations can be deployed swiftly to output without having going by a prolonged security audit every time. Chaillan estimates this approach has cut out one hundred hours of deployment hold off for his workforce in the last 12 months, and the workforce is in a position to make multiple entirely accredited software program variations for each working day.






